Recently, OpenClaw has become extremely popular.
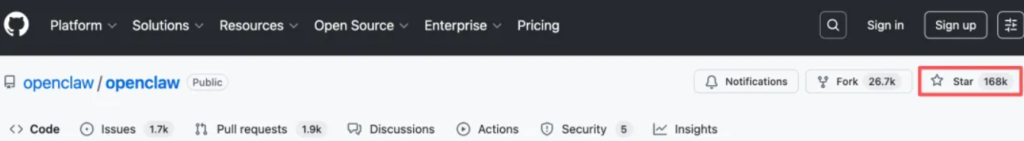
In just a few days, this open-source AI assistant with a red lobster logo, OpenClaw, has gained more than 160,000 stars on GitHub.
It is like a 24×7 online super employee. You only need to send instructions through chat tools such as WhatsApp or Telegram, and it can automatically handle emails, organize calendars, browse the web, manage files, and even execute code or complete complex tasks—a workflow that perfectly complements modern development practices like properly doing vibe coding.
But while it is popular, there are also many problems. Besides complex deployment and poor compliance, the most criticized issue is the frequent occurrence of security vulnerabilities.
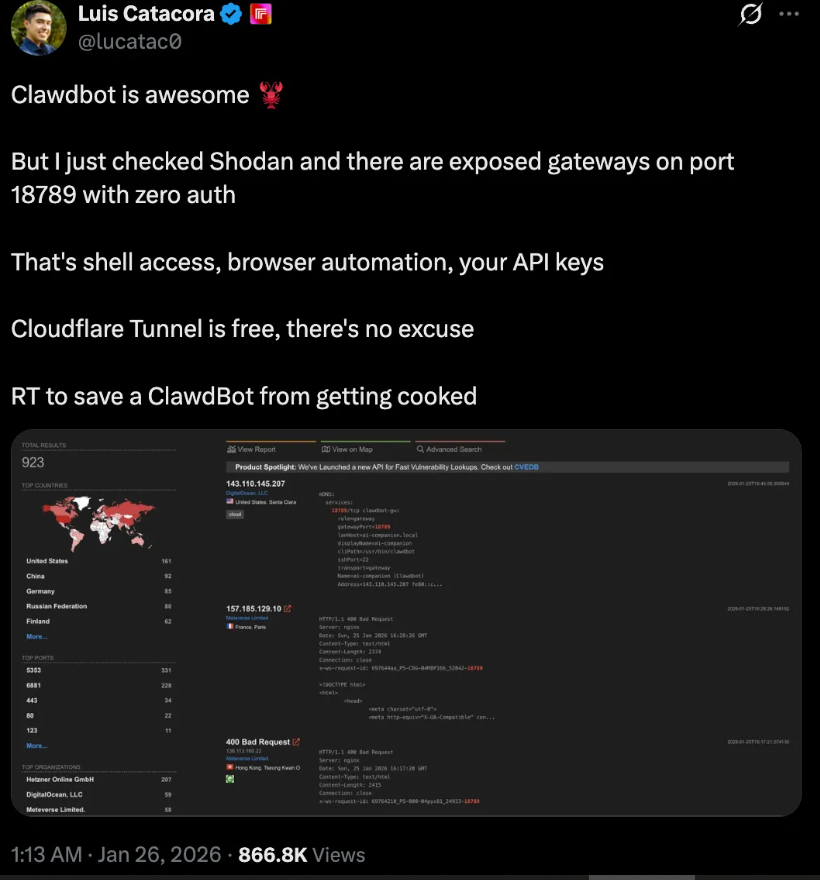
Some users searched on Shodan and found that many gateways running on port 18789 are open and have zero authentication, which may lead to shell access, browser automation interfaces, and API key leakage.
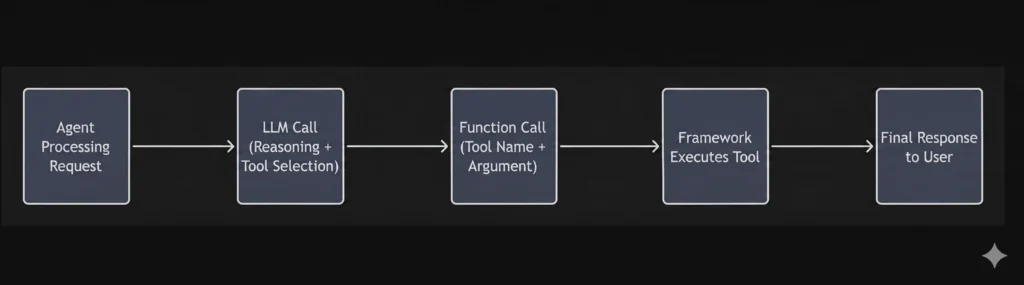
In fact, OpenClaw relies on a unified Gateway hub to schedule various local or remote tools to complete the above tasks. But the problem also lies here. When the Gateway lacks unified governance and tool calls lose control, security risks increase sharply.
Therefore, we can draw a conclusion: OpenClaw shows impressive innovation value at the Agent application level and is very suitable for exploration and testing, but it is not yet suitable for enterprise production environments.
OpenClaw’s Dilemma Reveals Enterprise Needs for Agent Tools
The dilemma of OpenClaw also reflects the real needs of enterprise-level Agents: not only powerful functions, but also security, controllability, easy integration, and scalable deployment. This is exactly the problem that Volcano Engine AgentKit aims to solve.
Volcano Engine AgentKit solves three core pain points in enterprise Agent deployment: tool fragmentation, inefficient calls, and security risks. It achieves this through AI reverse engineering to transform existing systems, MCP-based precise tool recall and governance to reduce token consumption, and Skills asset management with a zero-trust identity system.
These advantages have already been validated in real cases.
For example, in the retail industry, a nationwide chain retail group once faced huge operational pressure. The customer service team had to handle a large number of repetitive inquiries every day, and the information query process was fragmented. Customer service staff often needed to switch across more than 10 systems such as CRM, WMS, and OMS, and a single query could take up to 2 minutes.
By introducing AgentKit’s Tools solution, without modifying backend code, the company used MCP services to convert more than 50 core interfaces into intelligent tools with semantic descriptions. This “zero-modification” integration allows the Agent to understand complex user intent like an experienced employee.
When a user asks “What are the gifts for order A,” the Agent automatically decomposes the intent and sequentially calls order query, real-time inventory, and promotion rule tools, reducing the query time from minutes to seconds. At the same time, due to improved precision in tool calls, token consumption per interaction is reduced by 70%.
The same logic has also been verified in the fintech field. A cross-border payment company used AgentKit’s Skill Studio to package complex compliance and risk control strategies into executable Skills. Compliance experts can deploy skill packages such as “cross-border large transaction clustering analysis” without writing code, reducing regulatory response time from weeks to hours.
More importantly, each “decision report” generated by the Agent for suspicious transactions contains a clear reasoning trace, greatly reducing the pressure of compliance audits.
Why OpenClaw Highlights the Challenges of Agent Tools
Since Agent Tools are so useful, why are they only just beginning to land in enterprise scenarios?
This leads to three long-standing challenges: tool fragmentation, connection complexity, and governance black-boxing.
Enterprises do not lack tools. On the contrary, there are too many tools and they are chaotic. There are tens of thousands of existing APIs and legacy services, with different formats, incomplete documentation, and no unified interaction standards.
These tools are connected to core business data, so they cannot be ignored. However, the protocol for Agent interaction with external tools is MCP, while many enterprise services still use traditional HTTP APIs. If relying on manual reconstruction one by one, the development cycle can take months, which cannot keep up with business needs.
Even after connecting tools, another problem arises. When the number of tools grows to a certain scale, it becomes impossible to answer who is calling what, with what permissions, and whether the results are compliant. Traditional static API keys and long-term tokens cannot track the calling process, making auditing impossible. Tool calls become a black box, which enterprises cannot accept.
OpenClaw Context — Methodology for Designing Agent Tools
In response to these challenges, Volcano Engine summarizes key elements and methods for designing Tools across five stages of the Agent tool lifecycle.
From this perspective, Tools are the “senses” and “limbs” connecting large language models, such as the highly capable Claude Opus 4.7, to the real world. A qualified Agent Tool must be an interface that is understandable, secure, and fault-tolerant.
During development, developers should fully utilize Python’s type system, combine it with Pydantic BaseModel for parameter validation, and use Literal to restrict enum values, along with clear default values, to fundamentally prevent the model from “guessing blindly.”
At the interface design level, LLMs cannot understand APIs through technical documentation like traditional programs. As seen in improvements when comparing Claude Opus 4.7 vs Opus 4.6, models rely heavily on natural language descriptions to decide how to use tools. Therefore, developers need to invest significant effort in refining Docstrings, using Examples and Sample Cases to guide accurate parameter passing, and adhering to the “single responsibility” principle by splitting complex interfaces into smaller tools with clear parameters and responsibilities.
At the orchestration level, once MCP tools are clearly defined, developers need to think about how to combine independent tools into task flows. The key principle is task-oriented packaging and using a “progressive disclosure” strategy to dynamically provide relevant tools based on task progress, avoiding confusion caused by tool overload.
When tools enter execution, building self-repair capabilities becomes critical. Tools should not directly throw exceptions when errors occur but should return structured information with repair suggestions, allowing plugins to intercept errors and guide the Agent to retry automatically.
To ensure security, a Human-in-the-loop mechanism is essential. Sensitive operations must be confirmed by humans before execution. At the same time, performance optimization methods such as asynchronous calls and result summarization can effectively prevent context overflow and ensure fast response even in complex tasks.
OpenClaw vs Enterprise Solutions — AgentKit’s Three Core Capabilities
Methodology solves how to design tools well, while AgentKit focuses on how to implement them at scale in enterprise scenarios.
AgentKit builds a new Gateway hub that handles high-concurrency traffic, supports millions of QPS, and solves a key problem: how to make Agents understand enterprise legacy interfaces.
The AgentKit Gateway provides an intelligent “AI converter,” significantly lowering the barrier for enterprise AI transformation. Users can upload Swagger/OpenAPI documents or code, and the model automatically generates Tool Definitions that conform to MCP standards, filling in missing parameter descriptions and usage explanations.
At the same time, test cases are automatically generated to simulate Agent calls and verify whether the tool works and whether the return format is standardized. After conversion, tools can be hot-loaded into the Gateway without modifying business code.
This intelligent transformation reduces costs by 80% compared to manual reconstruction. The probability that AI-generated prompts are correctly understood exceeds 95%, and the automation rate of converting historical APIs into MCP tools reaches 90%. Managing these efficiencies is critical for enterprise budgets, much like carefully evaluating クロード 作品4.7 価格設定 when deploying models at scale.
As the number of tools increases, ensuring precise and efficient calls becomes critical. AgentKit Gateway acts as a central hub to achieve unified governance across traffic, control, and data layers.
At the traffic layer, all calls—whether Agent-to-MCP, Agent-to-Agent, or Agent-to-model—are uniformly processed. At the control layer, the Gateway console allows configuration of MCP routing, model routing, load balancing strategies, rate limiting, and security. At the data layer, all metadata related to Agents, including MCP, API, and Skills metadata, is managed in a unified lifecycle.
To address context redundancy, high token consumption, and hallucination issues in native MCP calls, AgentKit introduces a tool search and recall mechanism. Users can customize combinations of MCP tools and use tag-based search to progressively expand tools based on scenarios and categories, improving efficiency and accuracy.
Test data shows that under complex workloads with 50+ tools, token usage drops by 70%. With schema optimization, parameter accuracy for complex tool calls reaches 98.5%, and semantic caching improves response speed by 300%.
To improve reuse and management, AgentKit introduces the Registry component to centrally manage MCP, Skills, and other resources.
At the same time, Skills are introduced as core enterprise digital assets. They are fully compatible with Claude Code Skills while adding enterprise-level management capabilities.
AgentKit provides full lifecycle management for Skills, from development and testing to release and decommissioning. Through platform capabilities, Skills management is divided into generation, management, discovery, and execution.
Developers can use a built-in skill-creator to convert SOPs, templates, and scripts into reusable Skills packages. These are then registered, updated, and versioned in the Skills center, solving issues of cross-team sharing, version confusion, and unclear permission boundaries. Finally, the Skills Sandbox loads Skills on demand, interacts with LLMs for decision-making, and executes tasks in an isolated environment.
OpenClaw and Security — Identity and Zero-Trust Architecture
Security is a critical barrier for Agents entering enterprise production environments.
In autonomous execution scenarios, risks arise because Agents can perform multi-step, cross-system tool calls without human confirmation. An out-of-control Agent may execute multiple sensitive operations within seconds, while traditional authentication systems cannot track who initiated the call, under what conditions, and with what permissions.
AgentKit Identity redefines identity and permissions during runtime. By introducing Agent Persona and Delegation Chain, it applies zero-trust policies to every tool call, ensuring control, traceability, and auditability.
Specifically, AgentKit replaces long-term keys with dynamic temporary credentials and combines them with end-to-end delegation chains for fine-grained authorization.
The delegation chain binds the end-user identity, Agent Persona, and session or task context into a verifiable identity chain, which is securely transmitted during tool calls.
This ensures that every tool call verifies the complete delegation chain, aligning permissions with the actual executor and achieving true least-privilege principles and full accountability.
The Future After OpenClaw — Enterprise-Grade Agent Evolution
At the beginning of 2026, the surge of Agents triggered by OpenClaw shows the possibility of Agents entering the physical world. However, when applied in enterprise scenarios, this possibility often turns into significant security concerns.
Although this open-source project presents an attractive vision, its underlying architecture has clear shortcomings in privacy protection and permission control, even raising concerns about illegal usage in the community.
Volcano Engine AgentKit explores a more complete solution.
As an enterprise-level AI Agent lifecycle platform, AgentKit provides infrastructure capabilities such as runtime, memory/knowledge base, built-in tools, gateway, and identity, helping enterprises safely develop, deploy, and operate Agents.
Through a zero-trust architecture and dynamic credential mechanisms, AgentKit builds a reliable security layer for every tool call, making Agent systems more suitable for enterprise deployment.
Based on this infrastructure, Volcano Engine will launch enterprise-level intelligent assistants integrating CUA, MCP, and prebuilt Skills, along with human-in-the-loop authorization, fine-grained IAM, and persistent workspace mechanisms. This will drive AI from personal assistants toward responsible, process-driven enterprise “digital employees.”
Looking ahead, competition among Agents will shift from intelligence to toolchains. Large models provide the reasoning foundation, while production-ready Agent Tools determine the depth of business implementation.
What enterprises need is a governance hub like AgentKit that can unify traffic, control, and data, transforming existing digital capabilities into assets that Agents can use flexibly, and defining new competitive rules in the AI-driven era.
FAQ: OpenClaw — Use Cases, Safety, Cost, and Key Questions
What is OpenClaw used for?
OpenClaw is used to automate real-world tasks through chat-based commands. It can handle emails, manage calendars, browse websites, organize files, and execute code, acting like a 24/7 AI agent.
Is OpenClaw the same as ClawdBot?
No. OpenClaw is the open-source AI agent framework, while “ClawdBot” usually refers to a deployed instance or user-created version built on top of OpenClaw.
Is OpenClaw safe to use?
Not fully. OpenClaw has known security risks, including exposed gateways with no authentication, which can lead to API key leaks, shell access, and unauthorized control. It is safer for testing than production use.
Is OpenClaw free or paid?
OpenClaw is free and open-source. However, running it may require paid services such as AI model APIs, cloud hosting, or third-party tools.
How expensive is it to run OpenClaw?
Costs depend on usage. Main expenses include API calls, server infrastructure, and automation workflows. Light usage may cost a few dollars, while heavy workloads can scale much higher.
What is the 30% rule for AI?
The 30% rule suggests AI can reliably automate around 30% of structured or repetitive tasks, while the remaining work still requires human judgment, oversight, and validation.
Is there a free version of OpenClaw?
Yes. The core version of OpenClaw is free. Additional costs only come from the services and infrastructure you choose to use with it.
What does it cost to run OpenClaw?
Typical costs include:
- AI model API usage
- Cloud or local server resources
- Optional integrations and tools
Total cost varies widely based on scale and usage.
Does OpenClaw require a subscription?
No. OpenClaw itself does not require a subscription, but many supporting services (like AI APIs or cloud platforms) may charge based on usage or subscription plans.